In Word documents, headers and footers are crucial components that show consistent information at the top or bottom of each page, including page numbers, document titles, and company names. Manual processes can be ineffective when handling big document quantities or inserting headers and footers in batches. Using C# to automate these tasks can significantly improve document processing efficiency.
This article shows how to use C# and the Spire to create and modify headers and footers in Word documents.Common functions like adding text, graphics, and page numbers, as well as creating distinct headers and footers for odd and even pages, are covered by the Doc library.

Environment Setup
First, install the Spire.Doc package via NuGet:
Install-Package Spire.Doc
Or using the .NET CLI:
dotnet add package Spire.Doc
After installation, add the following namespaces to your C# code:
using Spire.Doc;
using Spire.Doc.Documents;
using Spire.Doc.Fields;
using System.Drawing;
Basic Concepts
Before writing code, it's important to understand several key concepts:
- Section: A Word document consists of one or more sections, each with its own header and footer settings
- Header: The area located at the top of the page
- Footer: The area located at the bottom of the page
- Paragraph: Content in headers and footers is organized and displayed through paragraphs
Adding Basic Headers and Footers
The following example demonstrates how to add headers and footers containing text and images to a Word document:
using Spire.Doc;
using Spire.Doc.Documents;
using Spire.Doc.Fields;
using System.Drawing;
// Create a document object and load the file
Document document = new Document();
document.LoadFromFile("Sample.docx");
// Get the first section
Section section = document.Sections[0];
// Get header and footer objects
HeaderFooter header = section.HeadersFooters.Header;
HeaderFooter footer = section.HeadersFooters.Footer;
// Add a paragraph to the header
Paragraph headerParagraph = header.AddParagraph();
// Add an image to the header
DocPicture headerPicture = headerParagraph.AppendPicture(Image.FromFile("Header.png"));
// Set image size and position
headerPicture.Width = 40;
headerPicture.Height = 40;
headerPicture.TextWrappingStyle = TextWrappingStyle.InFrontOfText;
headerPicture.HorizontalAlignment = ShapeHorizontalAlignment.Left;
headerPicture.VerticalAlignment = ShapeVerticalAlignment.Outside;
// Add text to the header
TextRange text = headerParagraph.AppendText("Internal Company Document");
text.CharacterFormat.FontName = "Arial";
text.CharacterFormat.FontSize = 10;
text.CharacterFormat.Italic = true;
// Set header paragraph right alignment
headerParagraph.Format.HorizontalAlignment = HorizontalAlignment.Right;
// Add bottom border line
headerParagraph.Format.Borders.Bottom.BorderType = BorderStyle.Single;
headerParagraph.Format.Borders.Bottom.Space = 0.05f;
// Add a paragraph to the footer
Paragraph footerParagraph = footer.AddParagraph();
// Add page number field
footerParagraph.AppendField("page number", FieldType.FieldPage);
footerParagraph.AppendText(" / ");
footerParagraph.AppendField("number of pages", FieldType.FieldNumPages);
// Set footer paragraph center alignment
footerParagraph.Format.HorizontalAlignment = HorizontalAlignment.Center;
// Save the document
document.SaveToFile("HeaderAndFooter.docx", FileFormat.Docx);
document.Dispose();
Below is the generated document's header and footer:

This code first loads an existing Word document, then retrieves the first section. The header and footer objects are accessed through the HeadersFooters property, paragraphs are added using the AddParagraph() method, and images and text content are added via the AppendPicture() and AppendText() methods.
Setting Different Headers and Footers for Odd and Even Pages
In formal documents, it's often necessary to set different headers and footers for odd and even pages. For example, odd pages may display chapter titles while even pages display the document name. The following code demonstrates how to implement this functionality:
using Spire.Doc;
using Spire.Doc.Documents;
using Spire.Doc.Fields;
// Load the document
Document doc = new Document();
doc.LoadFromFile("MultiplePages.docx");
// Get the first section
Section section = doc.Sections[0];
// Enable different headers and footers for odd and even pages
section.PageSetup.DifferentOddAndEvenPagesHeaderFooter = true;
// Add odd page header
Paragraph oddHeaderPara = section.HeadersFooters.OddHeader.AddParagraph();
TextRange oddHeaderText = oddHeaderPara.AppendText("Odd Page Header - Chapter Title");
oddHeaderPara.Format.HorizontalAlignment = HorizontalAlignment.Center;
oddHeaderText.CharacterFormat.FontName = "Arial";
oddHeaderText.CharacterFormat.FontSize = 10;
// Add even page header
Paragraph evenHeaderPara = section.HeadersFooters.EvenHeader.AddParagraph();
TextRange evenHeaderText = evenHeaderPara.AppendText("Even Page Header - Document Name");
evenHeaderPara.Format.HorizontalAlignment = HorizontalAlignment.Center;
evenHeaderText.CharacterFormat.FontName = "Arial";
evenHeaderText.CharacterFormat.FontSize = 10;
// Add odd page footer
Paragraph oddFooterPara = section.HeadersFooters.OddFooter.AddParagraph();
TextRange oddFooterText = oddFooterPara.AppendText("Odd Page Footer");
oddFooterPara.Format.HorizontalAlignment = HorizontalAlignment.Center;
// Add even page footer
Paragraph evenFooterPara = section.HeadersFooters.EvenFooter.AddParagraph();
TextRange evenFooterText = evenFooterPara.AppendText("Even Page Footer");
evenFooterPara.Format.HorizontalAlignment = HorizontalAlignment.Center;
// Save the document
doc.SaveToFile("OddAndEvenHeaderFooter.docx", FileFormat.Docx);
doc.Dispose();
The generated document's header and footer are shown below:

Setting the DifferentOddAndEvenPagesHeaderFooter property to true is crucial. Next, use the OddHeader, EvenHeader, OddFooter, and EvenFooter properties to access and modify the headers and footers for odd and even pages independently.
Changing the Header and Footer of the First Page
Certain papers call for either no headers and footers on the first page or specific headers and footers. This can be accomplished in the manner described below:
using Spire.Doc;
using Spire.Doc.Documents;
using Spire.Doc.Fields;
// Load the document
Document doc = new Document();
doc.LoadFromFile("Sample.docx");
// Get the first section
Section section = doc.Sections[0];
// Enable different first page header and footer
section.PageSetup.DifferentFirstPageHeaderFooter = true;
// Set first page header (can be left empty to hide header on first page)
Paragraph firstHeaderPara = section.HeadersFooters.FirstPageHeader.AddParagraph();
TextRange firstHeaderText = firstHeaderPara.AppendText("First Page Specific Header");
firstHeaderPara.Format.HorizontalAlignment = HorizontalAlignment.Center;
// Set regular header (for pages other than the first page)
Paragraph headerPara = section.HeadersFooters.Header.AddParagraph();
TextRange headerText = headerPara.AppendText("Regular Header");
headerPara.Format.HorizontalAlignment = HorizontalAlignment.Right;
// Save the document
doc.SaveToFile("FirstPageHeader.docx", FileFormat.Docx);
doc.Dispose();
The generated document's header and footer are shown below:
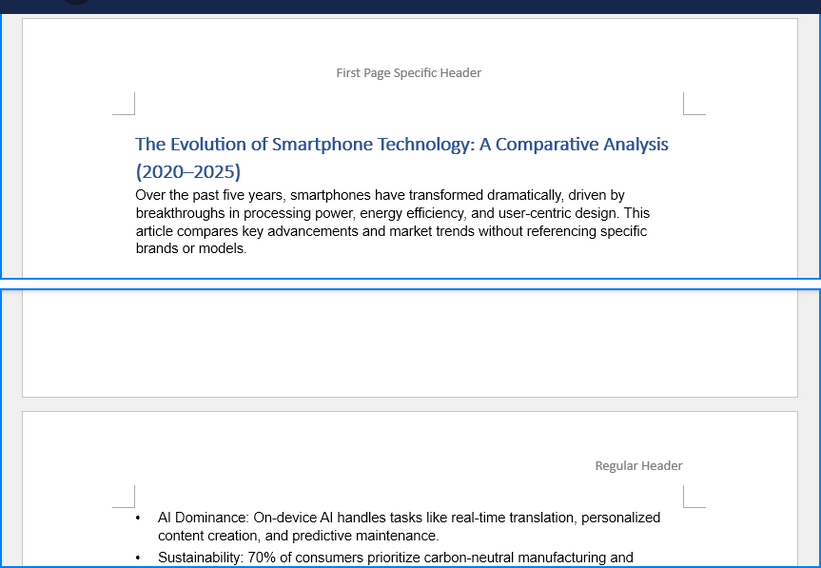
The FirstPageHeader and FirstPageFooter properties can be used to set the header and footer of the first page by setting the DifferentFirstPageHeaderFooter attribute to true.
Changing the Height of the Header and Footer
The HeaderDistance and FooterDistance properties allow you to change the height of headers and footers:
By setting the DifferentFirstPageHeaderFooter property to true, the first page's header and footer can be set using the FirstPageHeader and FirstPageFooter properties.
Adjusting Header and Footer Height
The height of headers and footers can be adjusted through the HeaderDistance and FooterDistance properties:
using Spire.Doc;
using Spire.Doc.Documents;
// Load the document
Document doc = new Document();
doc.LoadFromFile("Sample.docx");
// Get the first section
Section section = doc.Sections[0];
// Set the distance from the header to the top of the page (unit: points)
section.PageSetup.HeaderDistance = 50;
// Set the distance from the footer to the bottom of the page (unit: points)
section.PageSetup.FooterDistance = 50;
// Add header content
HeaderFooter header = section.HeadersFooters.Header;
Paragraph headerPara = header.AddParagraph();
headerPara.AppendText("Header with Adjusted Height");
// Save the document
doc.SaveToFile("AdjustedHeight.docx", FileFormat.Docx);
doc.Dispose();
Below is a preview of the generated Word document:
Practical Tips
Adding Page Number Formats
Page numbers are the most common element in footers and can be added in various formats:
Paragraph footerParagraph = footer.AddParagraph();
// Add "Page X" format
footerParagraph.AppendText("Page ");
footerParagraph.AppendField("page number", FieldType.FieldPage);
// Add "Page X of Y" format
footerParagraph.AppendText("Page ");
footerParagraph.AppendField("page number", FieldType.FieldPage);
footerParagraph.AppendText(" of ");
footerParagraph.AppendField("number of pages", FieldType.FieldNumPages);
Adding Separator Lines
Adding separator lines to headers or footers can enhance visual effects:
// Add separator line at the bottom of the header
headerParagraph.Format.Borders.Bottom.BorderType = BorderStyle.Single;
headerParagraph.Format.Borders.Bottom.Color = Color.Gray;
headerParagraph.Format.Borders.Bottom.LineWidth = 0.5f;
// Add separator line at the top of the footer
footerParagraph.Format.Borders.Top.BorderType = BorderStyle.Single;
footerParagraph.Format.Borders.Top.Color = Color.Gray;
footerParagraph.Format.Borders.Top.LineWidth = 0.5f;
Setting Image Size and Position
When adding images to headers and footers, the image position can be precisely controlled:
DocPicture picture = headerParagraph.AppendPicture(Image.FromFile("Logo.png"));
// Set image size
picture.Width = 40;
picture.Height = 40;
// Set text wrapping style
picture.TextWrappingStyle = TextWrappingStyle.Behind;
// Set horizontal position
picture.HorizontalOrigin = HorizontalOrigin.Page;
picture.HorizontalAlignment = ShapeHorizontalAlignment.Left;
// Set vertical position
picture.VerticalOrigin = VerticalOrigin.Page;
picture.VerticalAlignment = ShapeVerticalAlignment.Top;
Summary
This article has introduced various methods for adding and customizing headers and footers in Word documents using C#, including adding text and images, setting different headers and footers for odd and even pages, special handling for the first page, adjusting height, and other common operations. These techniques enable efficient batch processing of documents and automated header and footer configuration.
In practical applications, these methods can be combined according to specific requirements. For example, professional headers and footers containing company logos, document titles, and page numbers can be created for formal reports, or different header and footer styles for odd and even pages can be set up for book typesetting. Mastering these techniques can significantly improve the efficiency and standardization of document processing.